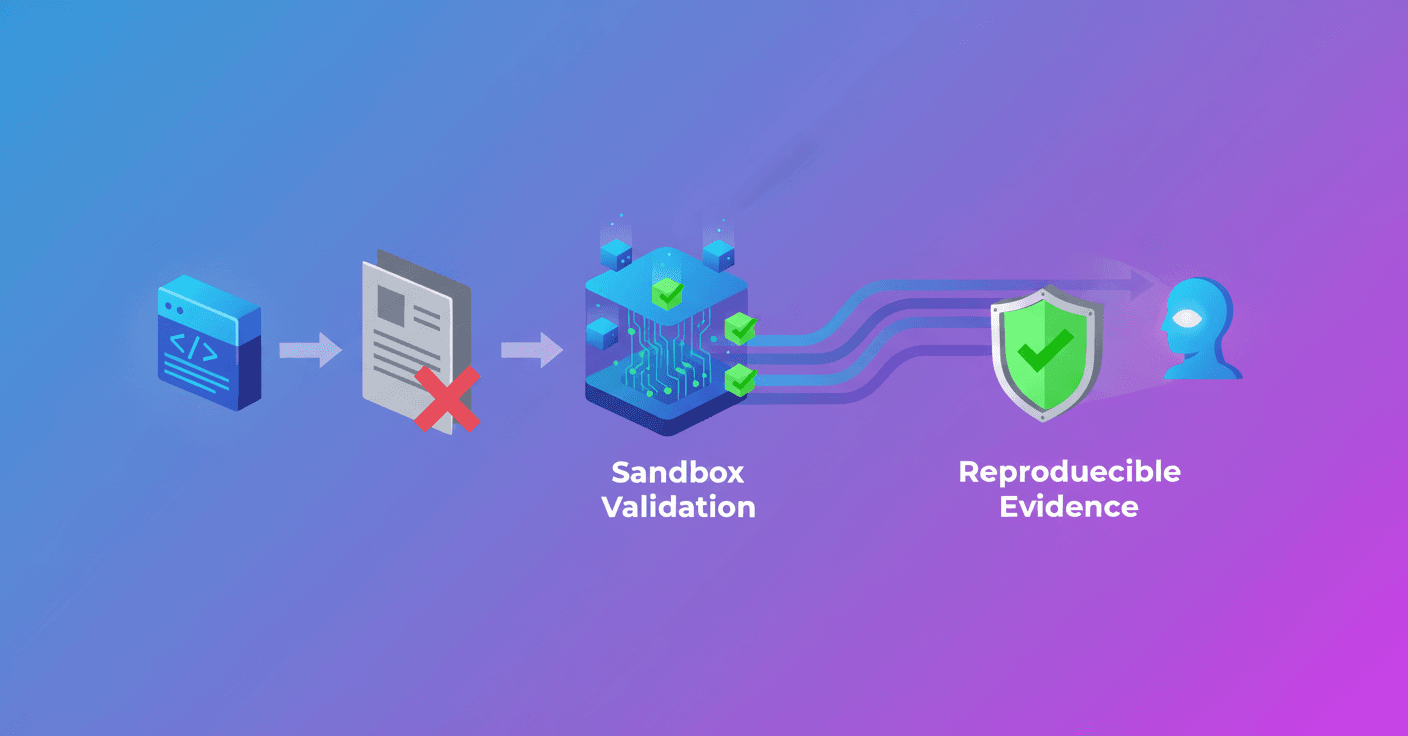
When you read that a security tool doesn't start with a SAST report it can sound odd: isn't SAST the classic way to scale code reviews? Codex Security made that decision on purpose because the reality of practical vulnerabilities is often more subtle than a simple data flow.
The root of the problem: validate intent, not just the flow
SAST does one very useful thing: it traces an untrusted input to a sensitive sink and marks the path. It's elegant and catches many mistakes. But is that enough to decide whether the system is actually secure?
The key point is that many failures are not just data flow issues. They're about intent and how checks hold up after transformations, decodings or normalizations. In other words: it's not enough to see that the code calls sanitize_html(); you need to prove that call preserves the invariant the system requires.
Sound familiar? A common case: you receive a redirect_url, apply a regex to allow only certain destinations, do a and then redirect. A source-to-sink report can show the route: input → regex → decode → redirect. But the real question is this: is the validation applied to the value that the redirect handler ultimately interprets? If the regex runs before the decode, the check might not restrict what is really interpreted afterwards.